“Information is the commodity of kings.” The quote is attributed to Tony Robbins, but surely it has been an axiom for as long as we’ve had royalty. Just as we secure other valuables like money or jewelry, we also need to secure our information.
The best way to secure information is to make it meaningless to others. We do that through encryption. We don’t have the money businesses and governments have to encrypt software, so we’ll have to look at free encryption software. Just because it’s free, doesn’t mean it’s bad. So we present to you the best free encryption software.
About Encryption
You know that encryption means making data unreadable unless you have the key. What you might not know is the different methods, or algorithms, used to encrypt data.
Encryption Keys
Think of an encryption key as an advanced sort of password. The difference is that encryption keys are often very long and random. You’ll often see them referred to as 128-bit or 256-bit keys, a number evenly divisible by 8. The number refers to how many bits make up the key or the length of the key.
While a password gets you into something, an encryption key is also part of the process of encrypting and decrypting data. What the encrypted data looks like is dependent on the key.
For data that only you will access, symmetric keys work best. It’s called symmetric because the key works on both sides – encryption and decryption. Key length isn’t considered as important with this system as you should be the only one with the key and physical access to the data. The NSA requires 256-bit symmetric keys.
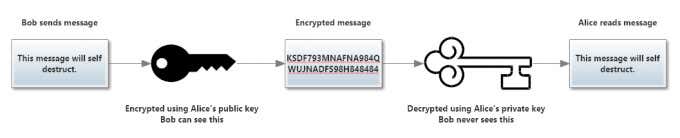
For sending or receiving data with other people, a symmetric key isn’t a good idea since the carrier would be able to decrypt the data. So an asymmetric key system is used. This means there is a public key and a private key. You share the public key with your friends to encrypt messages they send to you. The public key can only be used for encryption. Then you use the private key to decrypt the messages.
Asymmetric keys are normally longer than symmetric keys since the data is going out into the wild, where people can grab it and try to crack it. The longer the key, the less convenient it becomes. The National Institute of Science and Technology recommends 2048-bit keys.
AES – Advanced Encryption System
The most popular encryption algorithm, AES is the standard symmetric key encryption algorithm. AES encryption, using 128-bit keys, is sufficient for most people, but government agencies tend to use 256-bit or longer keys. This is the encryption you want for stationary data like USB flash drives, or hard drives.
RSA – Rivest Shamir Adleman Encryption
RSA is a public, or asymmetric, key encryption algorithm. The algorithm is used in different security protocols like OpenPGP and SSL certificates used with the HTTPS protocol. You’ll see these protocols using 1024-bit or 2048-bit keys. The latter is more popular. If you’re looking for secured communications, look for terms like RSA, HTTPS, PGP, OpenPGP, and GnuPG.
Best Free Encryption for Drives
Let’s start with the biggest store of information most of us have, the hard drives in our computers. We’re recommending two, depending on what operating system (OS) you use.
FileVault 2
OS: Apple OS X Lion and newer
Encryption Algorithm: XTS-AES 128-bit
Apple has a reputation for being protective of its customers’ data, so it’s no surprise they include FileVault with OS X. FileVault encrypts Mac’s startup drive using your login password as the encryption passphrase. That does make it more difficult to use on multi user Macs.
The drive has to be unlocked before anyone can use the Mac. If the user has unlock permissions, they’re fine. If they don’t, then someone else with unlock permissions must log in first, and then the other user can log in and work.
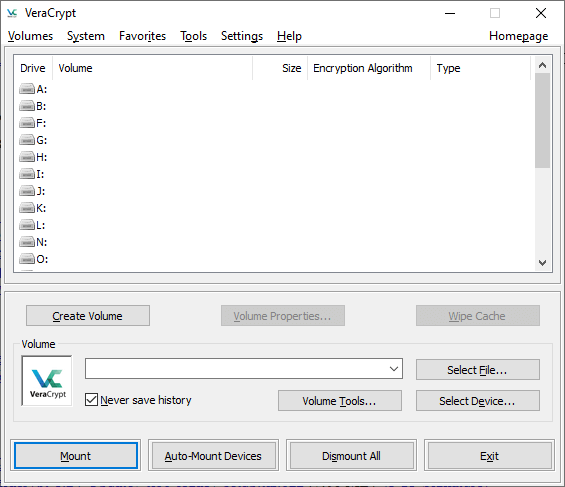
VeraCrypt
OS: Windows, OS X, Linux
Encryption Algorithm: AES 256-bit, Camellia, Kuznyechik, Serpent, Twofish, and variants
The open-source VeraCrypt is great for whole volume encryption. It uses on-the-fly encryption, meaning as data is written to the disk, it gets encrypted. At any point in time, everything is encrypted.
Besides being free and available for Windows, Mac, and Linux, VeraCrypt has the unique feature of creating a hidden encrypted volume inside the normal encrypted volume.
Why is this important? Imagine that you are compelled to decrypt your drive for some reason. That’s fine, go ahead. All of your really important files are in the hidden encrypted volume. Created properly, the hidden volume won’t be detectable at all, so if it doesn’t appear to exist you can’t be compelled to decrypt it. That’s probably more than most people need, but it is cool.
Best Free Cloud Encryption Software
Boxcryptor
OS: Windows, macOS, Android, iOS
Encryption Algorithm: AES 256-bit and RSA 4096-bit
When we put our files into cloud storage, we also put a lot of trust in the service provider to protect them. It’s not like we have the drive sitting in our house. How do we know someone else hasn’t accessed it or that the cloud service provider isn’t going through it? We don’t. That’s where Boxcryptor comes in.
The Boxcryptor agent lives on your computer and encrypts all data being sent up to your cloud storage, making it unreadable to anyone but you. When you open those files, Boxcryptor decrypts them without any extra steps. It just happens.
Boxcryptor works on Windows, macOS, Android, iOS, and even within Microsoft teams. It will integrate with most major cloud storage providers such as OneDrive, Google Drive, Dropbox, iCloud, SharePoint, and more. It’s free for individuals to use with one cloud provider and on 2 devices, which is enough for most people.
Best Free Secure Email with Encryption
ProtonMail
OS: Any computer with a web browser, has apps for iOS, and Android
Encryption Algorithm: PGP
Your email is protected by ProtonMail with technology and law. ProtonMail doesn’t keep logs of the activity or store IP addresses or any other data that may be used to identify you. Add the PGP encryption capability to that with 500MB of free storage and Protonmail is a formidable force for email security.
On top of that, Protonmail is based in Switzerland, known for chocolate, watches, and some of the strongest privacy laws in the world. That makes it more difficult for anyone to compel ProtonMail to release whatever data they may have, compared to most other countries.
Best Free Email Encryption Add-on Or Extension
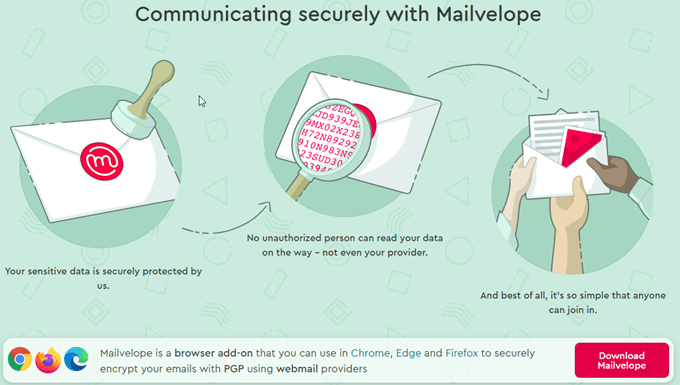
Mailvelope
OS: Any, runs in Chrome, Edge, and Firefox web browsers
Encryption Algorithm: OpenPGP
Not ready to leave your current email provider to get encryption? With Mailvelope, you don’t have to. Functioning as a browser add-on, Mailvelope gives you the ability to encrypt your emails with GnuPG and has USB token support.
You can keep your cryptographic key on a USB flash drive. This prevents anyone from getting your key unless they have physical access to it. Mailvelope is free for personal use, works in Firefox, Chrome, Edge, and Brave browsers, and all common webmail providers.
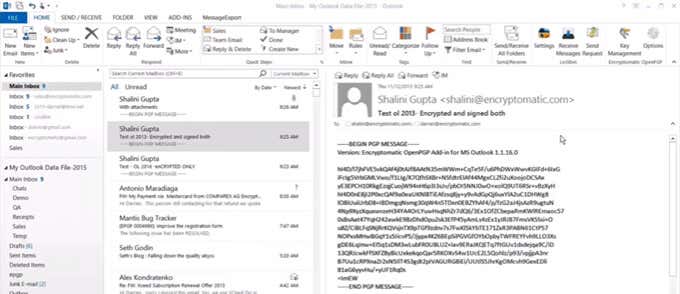
Encryptomatic
OS: Outlook on Windows 10
Encryption Algorithm: OpenPGP
Encryptomatic deserves an honorable mention as it provides an Outlook add-in to give you end-to-end OpenPGP encryption. It’s free for personal use, non-profits, and independent journalists. If you’re an avid Outlook user, you owe it to yourself to check out Encryptomatic. It makes email encryption as simple as a right-click.
Best Free Messaging Encryption
Signal
OS: Android, iOS, Windows, Mac, Linux
Encryption Algorithm: Signal Protocol – combines Double Ratchet algorithm, X3DH, Sesame Algorithm, XEdDSA and VXEdDSA signature schemes, AES 256-bit, and HMAC-SHA256
It’s been in the news a lot lately and we’ve written about it for secure messaging. Signal Private Messenger has provided free end-to-end encrypted messaging for years. At first, Signal only offered encrypted text messaging, but has grown to include encrypted voice and video calling.
There’s also a Signal desktop app for Windows, Mac, and Linux. It’s a fully encrypted communications suite endorsed by privacy advocate Edward Snowden and Twitter founder Jack Dorsey.
Best Free Browser Encryption Software
HTTPS Everywhere
OS: Any desktop using Firefox, Chrome, Edge, Opera, Brave, or Tor browsers
Android – Firefox, Brave, and Tor
iOS – Onion Browser
Encryption Algorithm: RSA
All interactions with a website can be transmitted over the Internet. During transmission, the data could be accessed anywhere between your computer and where the site is hosted. That’s why there’s such a push in the industry to make every website use the Hypertext Transfer Secure Protocol (HTTPS).
However, many sites can be accessed through regular Hypertext Transfer Protocol (HTTP). HTTPS Everywhere doesn’t do any encryption but it will force the browser to use the HTTPS version of a site if it exists in the DuckDuckGo Smarter Encryption dataset. That’s a database of over 12 million sites that are known to have HTTPS versions. If parts of a site come from web servers not using HTTPS, those parts will not be encrypted. HTTPS Everywhere can be installed in most major web browsers and is already included in the Brave and Tor browsers.
Best Free Security Certificate For Encryption
LetsEncrypt
OS: Any
Encryption Algorithm: RSA
At this time there’s only one free security certificate authority, so LetsEncrypt wins by default. Make no mistake, LetsEncrypt is still worthy of the title. All TLS certificates issued by LetsEncrypt must be domain-verified and the process can be automated using the Certbot ACME client.
Over 260 million websites are using certificates authorized by LetsEncrypt. Looking through the list of sponsors for LetsEncrypt is like looking through a Silicon Valley directory.
Start Encrypting
With some combination of the free encryption software listed here, you and your data will be more secure than most people in the world. Any amount of encryption is better than none because criminals look for the easiest fruit to pick. As soon as they come across encryption it better be a juicy payoff or it’s not worth the effort. So start encrypting now.