Prevent your identity from being stolen
In the bad old days, before everyone had a small supercomputer in their pockets, the only way for many people to get internet access was through an internet cafe. You’d show up, pay a few dollars and then get a computer all to yourself for a set amount of time.
These days, the use of public computers is relatively rare in the Western world. Regardless, there’s a good chance that, at some point, you’ll be put in a position where you need to use a public computer. Maybe your phone is dead or stolen? Maybe you are in another country and have no coverage or WiFi access? At this point that hotel or internet cafe computer might look like a lifesaver.

What you might not know is that public computers pose a significant privacy risk. So when the time comes, how can you minimize the dangers of using these innocuous-looking machines?
Why Are Public Computers a Risk?
First off, let’s clarify the exact risk these computers pose. The main problem with public computers is, well, they’re public. With your own personal devices you can count on pass codes, passwords and strong disk encryption to prevent anyone else from getting your sensitive information.
With a public computer whatever information you leave on the machine is waiting for the next user to do with as they please. That’s a real problem because with modern computing you’re leaving information left and right like digital dandruff. Usually without knowing it.
The other main risk of these machines comes from people who have used it before you sat down. Not just because the typical public mouse and keyboard is a bio-hazard, although that’s another issue, but because they could have left all sorts of nasty surprises for you.
These surprises are aimed at skimming information from you in a variety of ways. Which means you should really only use public computers as a last resort if its an emergency.
Check For Anything Suspicious

The first thing you should do is check whether there’s anything suspicious plugged into the machine. One common item is a USB keylogger device.
This is a USB device that sits between the keyboard and computer, and records every single keystroke made on that machine. The owner of the logger will come back at some later time to dump its logs. It will then search for email addresses, passwords and credit card numbers.
If you see anything weird plugged into the computer that you don’t recognize, it’s best to go elsewhere.
Browser Privacy Modes Are Your Friends

If you’re going to be browsing the web using the browser found on the computer, then you should definitely switch it to privacy mode. For example, in Google Chrome this is called incognito mode.
When you browse the web from a private Window, the browser doesn’t record any of your information permanently. When you close the window, all your browsing history, passwords, logins and other similar information will disappear.
Privacy mode doesn’t hide anything from the proxy server or ISP though. So don’t visit prohibited sites. If you want to hide your internet activity on a public computer you’ll need to use a VPN and perhaps also the Tor browser. However, that’s a slightly different discussion.
Portable Apps & Live Operating Systems
While using privacy mode on public browsers is a good piece of common sense in a pinch, it’s better to avoid using any of the software on that computer at all. Even better, you can avoid using the operating system in its entirety!
The first part of this puzzle comes in the form of portable apps. These are special applications that don’t require installation, are self-contained and run from any media. So you can load up portable applications on a flash drive and plug it into the public machine.
First among these should be a portable antivirus package. You may also want to add a portable browser and portable office suite.
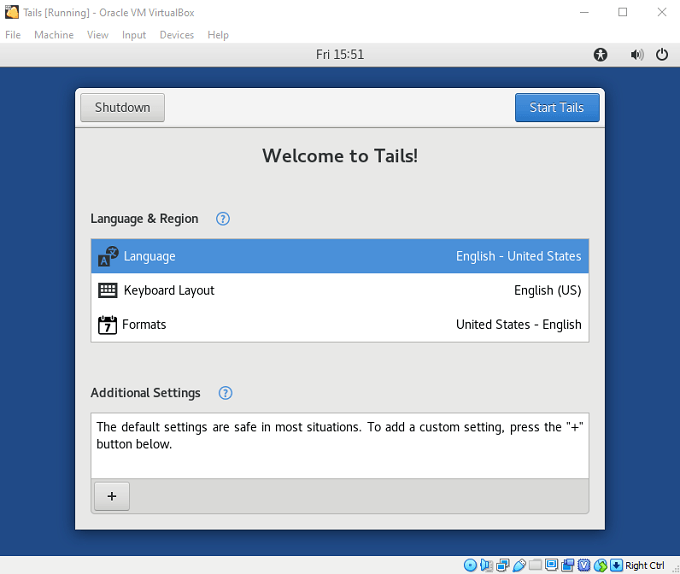
When it comes to skipping out on the public machine’s operating system, you can use portable virtual machine software, running a clean OS image of something like Linux. This has the advantage of not requiring a reboot.
If you are allowed to, you can also boot a live operating system from a flash drive or optical disc. Ensuring that none of your personal information ever touches the public machine’s permanent storage at all!
Clean Up After Yourself

Of course, using portable apps and live operating systems requires some forethought. You need to prep a flash drive, throw it in your bag and then hope you never need to use it. If you do end up in a situation where you had no choice but to use one of these computers without proper protection, you need to do some decontamination work afterwards.
You should make sure your entire browsing history and all browsing data has been removed. You might also want to run a free space file shredder on the machine to make sure your deleted information cannot be recovered. Likewise, make sure you didn’t leave anything in the computer’s recycle bin.
If you had to log into any services from that public computer, it’s a good idea to change your passwords at the first opportunity. If you didn’t already have two-factor authentication, you should also ensure it’s switched on for every service in question.
A Byte Of Prevention Is Better Than a Gig Of Cure
It might seem a little overblown to care this much about public computer safety. However, in a world of cybercrimes, identity theft and worse, taking just these few steps can be the key to keeping you safe from the harsh world of internet crime.
So prep that emergency flash drive today and make sure you’re never caught out when you’re already dealing with enough problems.